Get FREE Basic Computer Course for any 6 Months Course
Ethical Hacking is the authorized practice of bypassing system security to identify potential threats, vulnerabilities, and data breaches in a network or system. Ethical hackers use the same tools and techniques as malicious hackers but in a legitimate and lawful manner to help organizations strengthen their defenses. It plays a vital role in protecting sensitive data, applications, and infrastructure from cyberattacks.
Learning Ethical Hacking equips individuals and professionals with critical skills in penetration testing, vulnerability analysis, and cybersecurity defense. It creates strong career opportunities in information security, cyber forensics, and network defense. Students and professionals can build global careers as ethical hackers, security analysts, or consultants.
An Ethical Hacking course can be joined by students, IT graduates, job seekers, penetration testers, system administrators, cybersecurity professionals, developers, and entrepreneurs. Ideal for beginners and professionals to learn cybersecurity, ethical hacking, and global security skills.
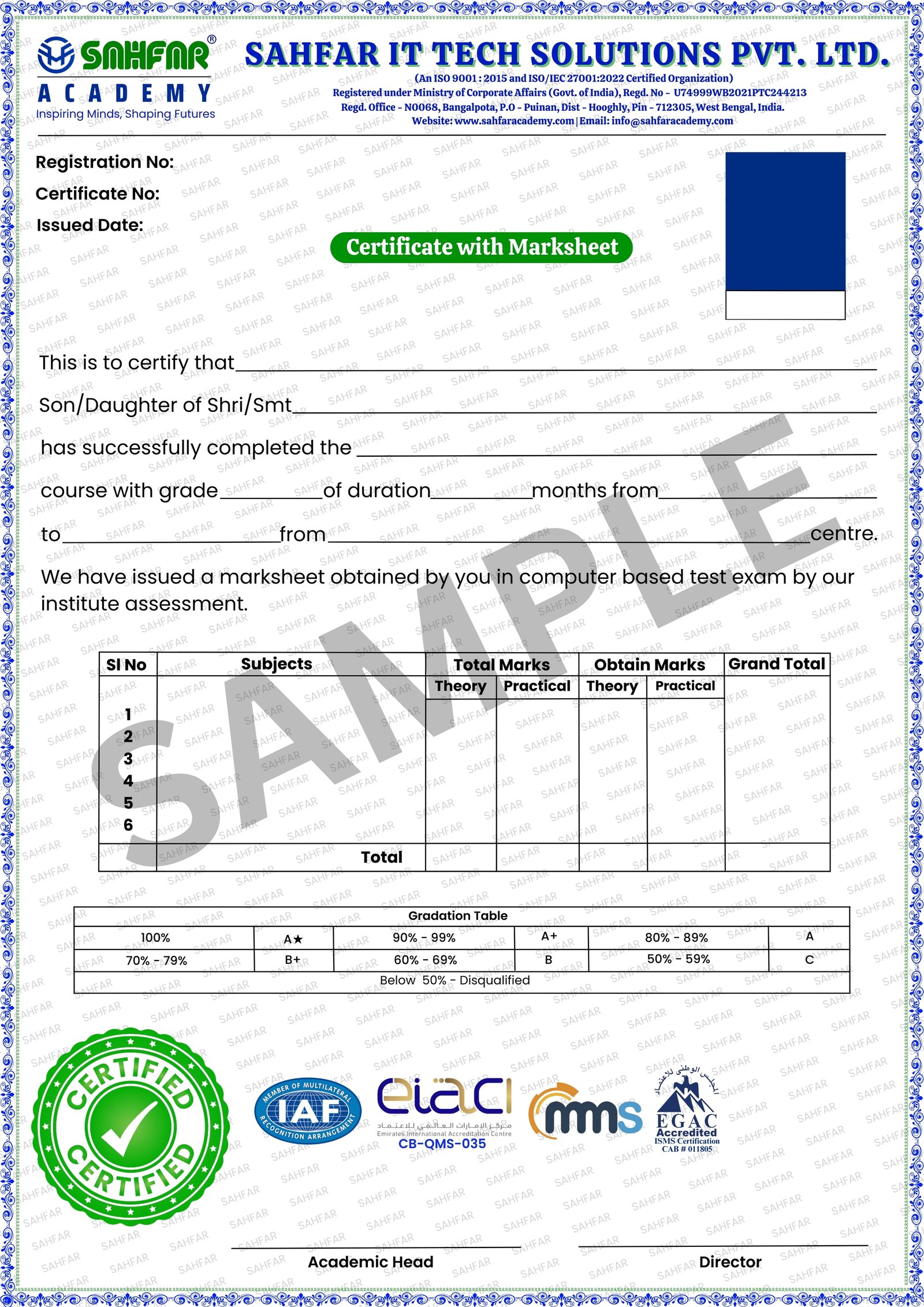
The SAHFAR ACADEMY Certification is designed to validate your skills with a perfect blend of practical training and theoretical knowledge. Our curriculum is aligned with real-world demands and reviewed by industry experts.
This certification is recognized by companies across India, making it a trusted mark of your capability. It reflects your readiness to take on professional challenges with confidence and clarity.
Whether you're starting your career or upskilling for better opportunities, our industry-graded certification ensures your learning meets professional standards and is accepted by leading startups, MSMEs, and corporate houses.
 Recognized by Industry Experts
Recognized by Industry Experts Adds Value to Resume
Adds Value to Resume Skill-Based Assessment
Skill-Based Assessment Proof of Course Completion
Proof of Course Completion Digital & Printable Format
Digital & Printable Format Career Accelerator
Career Accelerator"SAHFAR Academy’s Ethical Hacking course completely changed my career path. I learned real cybersecurity skills like penetration testing, network scanning, and vulnerability analysis. Trainers explained everything practically. Now I feel confident to apply for cybersecurity jobs and internships."

Cyber Security Fresher
"This 3 months Ethical Hacking course at SAHFAR Academy is very practical and beginner friendly. I had no technical background, but now I can use tools like Nmap and Metasploit confidently. The support from teachers is really helpful and motivating."

Student
"Best decision to join SAHFAR Academy for Ethical Hacking. The live lab setup and real-time practice on Kali Linux helped me understand concepts deeply. Trainers are always ready to solve doubts. I even started learning bug bounty after this course."

Freelancer
"SAHFAR Academy gave me strong foundation in cybersecurity. From networking basics to web security and attacks, everything was covered step by step. The practical approach and teacher guidance helped me gain real confidence in ethical hacking."

IT Support Executive
"I joined this course to upgrade my IT skills, but it exceeded my expectations. I learned scanning, exploitation, and web vulnerabilities practically. Trainers are very supportive and explain concepts clearly. This course really adds value to my career."

Working Professional
"SAHFAR Academy’s Ethical Hacking course is perfect for anyone serious about cybersecurity. The training includes real tools, real scenarios, and strong mentorship. After completing the course, I feel ready to start my career in the cybersecurity field."

Aspiring Ethical Hacker